Why London businesses need the right IT security consultant
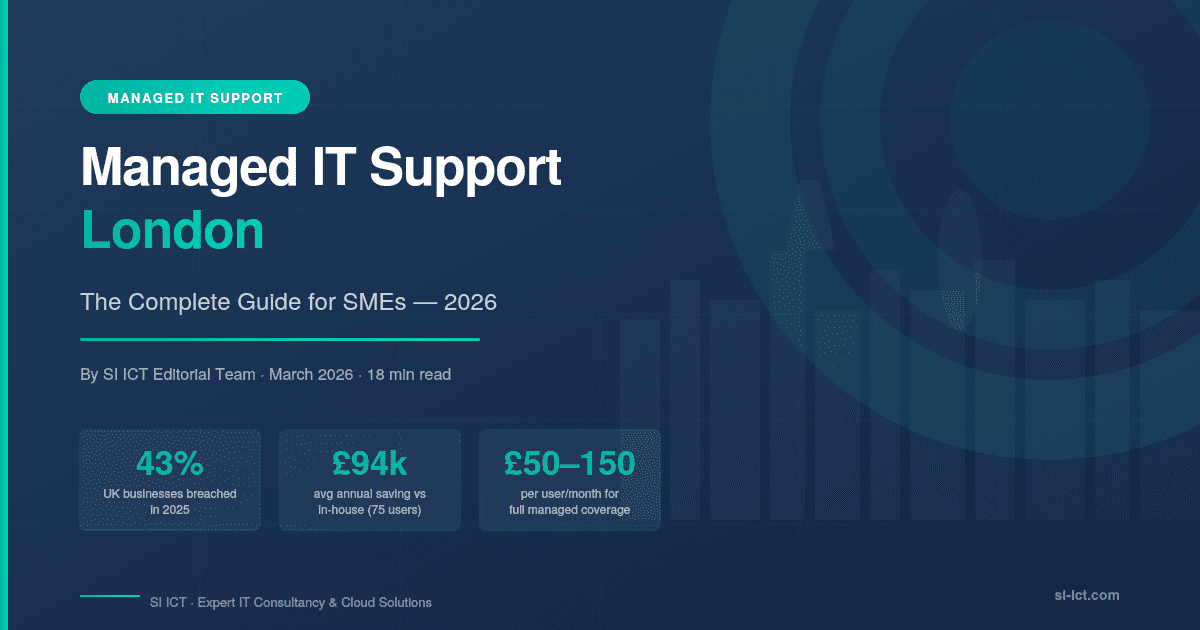
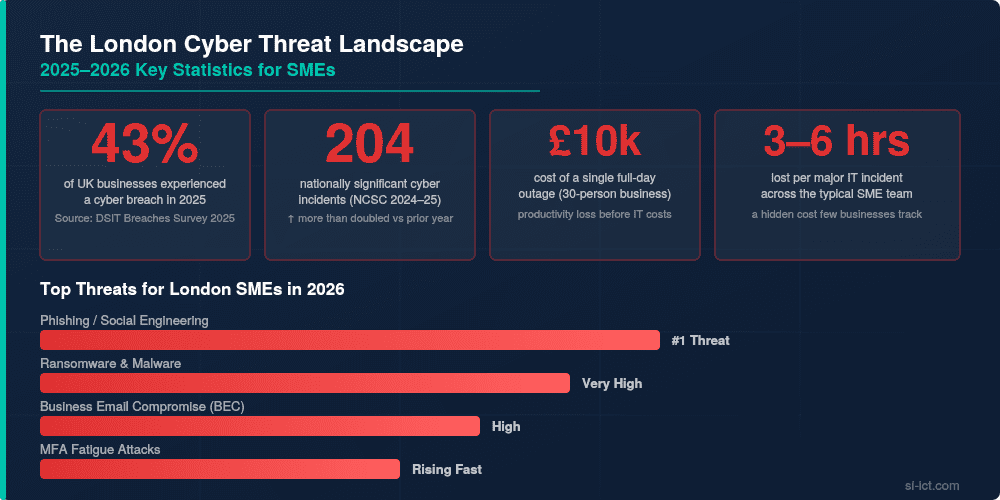
London businesses face a dense mix of financial, legal, tech and professional‑services targets, making the city a prime hunting ground for cybercriminals. Ransomware, business email compromise, data theft and insider threats can all hit reputation, operations and compliance in one blow.
A strong IT security consultant helps you understand your risk, design a realistic security strategy and then operate the technology that keeps you safe day and night. SI ICT specialises in this blend of consultancy and hands‑on protection through its 24×7 managed IT security operations centre, built around Microsoft Sentinel and XDR.
In the modern digital economy, data is more than just information—it is the lifeblood of your company. However, as London and UK businesses accelerate their digital transformation, the “attack surface” for hackers has expanded.
Finding the right partner among the sea of cyber security companies is no longer a luxury; it is a fundamental requirement for business continuity.
The State of Play: Why “Good Enough” IT Isn’t Enough
The “traditional” approach to security—a basic firewall and an expired antivirus—is effectively an open door to modern ransomware. Today’s threats are AI-driven, automated, and relentless.
What Modern Cyber Security Companies Actually Do
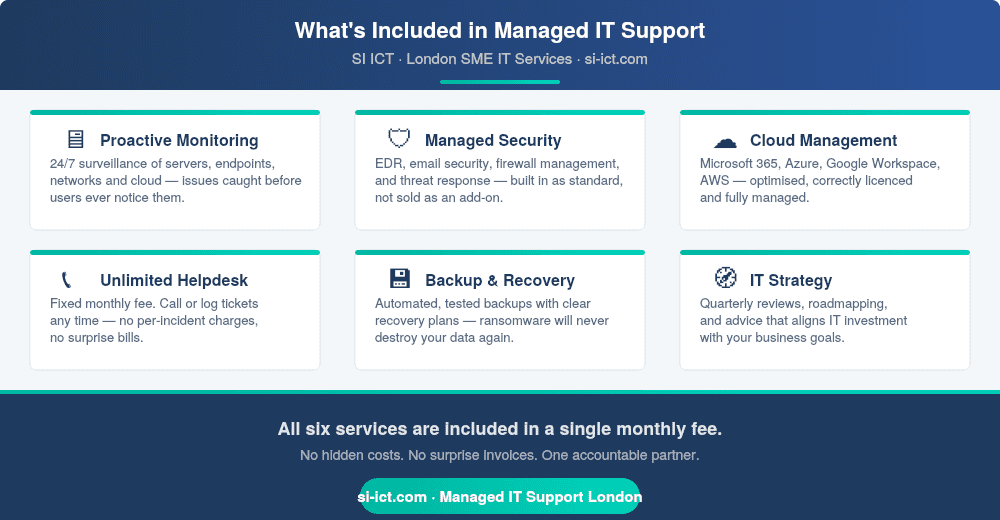
Leading providers like SI ICT moved beyond “reactive” support years ago. We focus on Proactive Resilience. This means identifying a threat before it hits your inbox, not cleaning up the mess after your servers are encrypted.
What a top IT security consultant actually does
Behind the buzzwords, an effective IT security consultant for London businesses delivers three things: visibility, control and response. They assess your current environment, align controls to recognised frameworks, and then help you operate, monitor and continuously improve your defences.
SI ICT’s managed IT security service is a good example of this full lifecycle. It combines design and architecture work with a 24×7 Security Operations Centre (SOC) that monitors telemetry from Microsoft 365, Azure, on‑premises networks and other critical systems, using Microsoft Sentinel to correlate signals into actionable incidents.
Key responsibilities typically include:
-
Security assessments and roadmap
Understanding your business, data flows, existing tools and threat profile, then producing a practical roadmap rather than a generic report. -
Architecture and control design
Designing secure configurations for identities, endpoints, networks, cloud services and applications, using principles like least privilege and assume breach. -
Implementation and integration
Deploying and tuning tools such as firewalls, endpoint protection, email security, SIEM/SOAR platforms and backup/DR solutions. -
24×7 monitoring and incident response
Running or augmenting a SOC to detect, investigate and respond to threats in real time, with clear escalation paths and recovery plans.
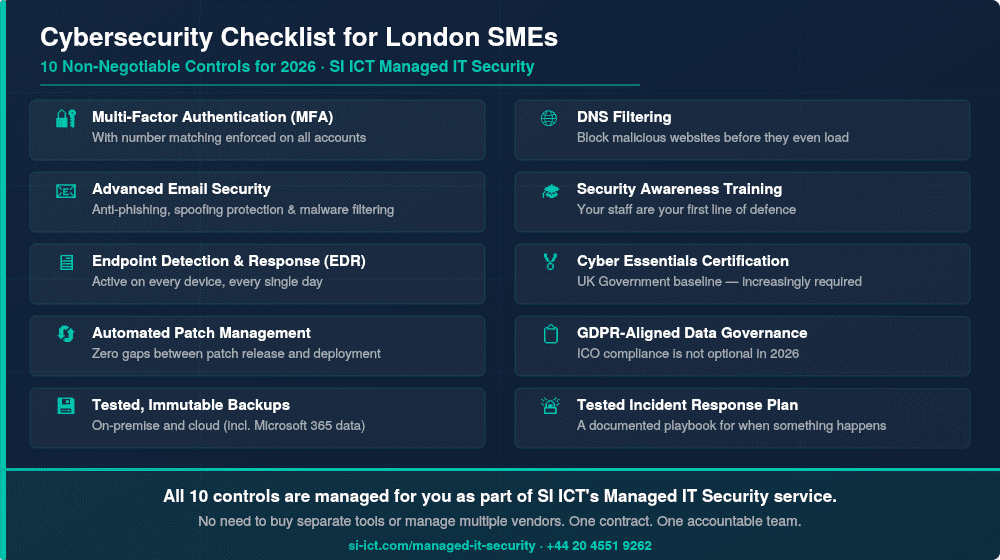
The 5 Pillars of Business Cyber Security
To secure your business, you must address these five core domains. Use this as your internal audit checklist:
1. Identity & Access Management (The New Perimeter)
With hybrid work, the “office wall” has disappeared. Your new perimeter is the user’s identity.
-
The Standard: Multi-Factor Authentication (MFA) is the bare minimum.
-
The Evolution: Zero Trust Architecture. This ensures that every login attempt, whether from a London boardroom or a home office in Surrey, is verified and encrypted.
2. Managed Detection and Response (MDR)
Cyber-attacks don’t happen during 9-to-5 office hours.
-
The Strategy: 24/7 “Eyes on Glass” monitoring. We use AI-integrated tools to spot unusual patterns, such as a login from an unknown country or a mass file-deletion event, and neutralize it instantly.
3. Business Continuity & “Immutable” Backups
It’s not a matter of if, but when. If your systems go down, how fast can you recover?
-
The Fix: Immutable backups. These are “read-only” copies of your data that hackers cannot delete or encrypt, ensuring you never have to pay a ransom.
4. Employee “Human Firewall” Training
90% of successful breaches start with a phishing email. Your staff are your strongest defence or your weakest link.
-
The Solution: Regular, bite-sized security awareness training and simulated phishing tests to keep security top-of-mind.
5. Compliance & Certification (Cyber Essentials)
For UK businesses, the Cyber Essentials certification is the gold standard. It proves to your clients and insurers that you have implemented the five technical controls required to stop 80% of common attacks.
Choosing Between Cyber Security Companies: The SI ICT Difference
Many companies provide security tools; SI ICT provides security strategy. We don’t believe in “set and forget.” Our London-based team acts as your virtual CISO (Chief Information Security Officer), ensuring your technology scales alongside your ambitions.
-
Local Expertise: We understand the UK GDPR landscape and ICO reporting requirements.
-
Bespoke Roadmaps: We audit your specific risks and build a plan that fits your budget.
-
Future-Proofing: We integrate AI-defences today to protect you against the threats of tomorrow.
Book Your Comprehensive Security Audit with SI ICT →
Get support for Cyber Security for your Businesses.
Book your introductory strategy session with an SI ICT consultant today to gain clarity and direction
Book a Free Strategy Session Consultation with SI ICT